Applications of the Internet of Things (IoT) are still growing across all industry verticals, and they are moving away from isolated IoT device clusters and toward interconnected IoT environments. This is especially evident in settings like automobiles and factory floors. However, the Internet of Things (IoT) industry has not yet achieved a truly seamless experience in which devices enter and exit physical environments that are identified, trusted, and managed without the need for separate (sometimes manual) authentication steps. Additionally, the IoT has not yet scaled as quickly as anticipated.
Opportunities exist for a variety of value chain participants as a result of the increasing complexity of IoT use cases, such as transportation and autonomous systems, and the proliferation of connected devices. However, it also raises the possibility of vulnerabilities that could lead to catastrophic outcomes. Due to the IoT’s control over physical operations, many IoT systems have risk profiles that are higher than those of enterprise IT.
This safe and seamless experience is not supported by traditional IoT security strategies. In today’s IoT solution designs, buyers report that there is little multilayered security. Vulnerabilities arise as a result, necessitating regular over-the-air updates and patches that cannot be reliably implemented. For this reason, companies look for reliable IoT solution providers.
With industry leaders, we tested our hypothesis regarding the significance of cybersecurity and IoT convergence and discovered yet another significant result. Concerns about expected IoT adoption, digital privacy, and trust, as well as the delay caused by siloed decision-making leads, are widely misunderstood by IoT buyers and providers. Future technology leaders on both the provider and buyer sides should be able to gain a better understanding of the mindsets of others and work toward unlocking the value by having some knowledge of some of these facts.
According to our findings, IoT solution providers are more optimistic than IoT buyers regarding the likelihood of achieving a seamless experience soon. Even in the early stages of IoT implementation, they are running into difficulties. Interoperability, cybersecurity, and installation complexities are their primary concerns.
When compared to customers, IoT solution providers greatly undervalue the significance of digital trust; In contrast to the approximately 60% of buyers who regard digital trust as essential in IoT solutions, only 30% of providers consider it to be so. To address their cybersecurity concerns, however, IoT buyers require more cohesive decision-making structures. Eighty-one percent of providers hold the view that siloed decision-making between the IoT and cybersecurity groups on the buyer end is to blame for IoT adoption delays. On the other hand, only 42% of buyers believe that the decisions are made independently.
Based on these insights, we have concluded that to build user confidence in the Internet of Things, accelerate its adoption, and drive new value across its verticals—thereby creating a fully interconnected IoT environment—it will require a significant shift in the philosophy of IoT solution design as well as a holistic convergence of IoT and cybersecurity functionalities. Increased policymaking at the public and private levels further supports these market forces. It will be possible for technology leaders to influence disruptive change for consumer and enterprise applications if they understand the necessary mindset.
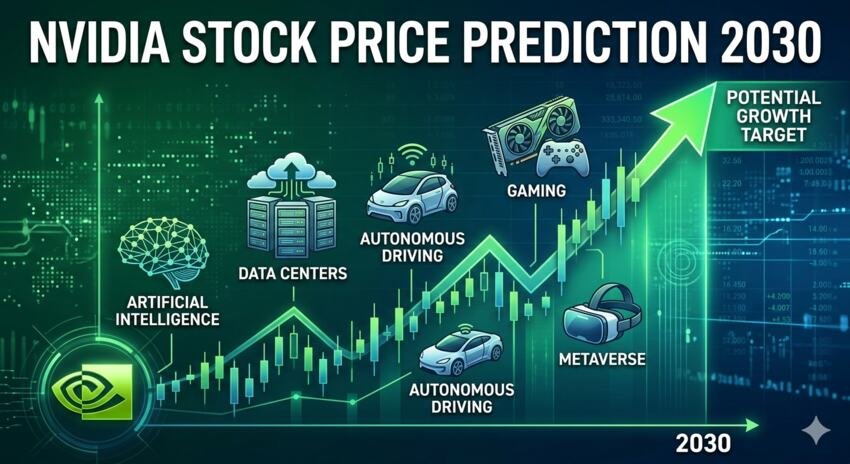
The rewards could be enormous if the industry can combine cybersecurity and the Internet of Things. In a baseline scenario, it is anticipated that the market for IoT suppliers will reach approximately $500 billion by 2030. Executives would spend 20% to 40% more on the Internet of Things if cybersecurity concerns were completely managed. Also, an extra five to ten rate points of significant worth for IoT providers could be opened from new and arising use cases. This suggests that IoT suppliers’ total addressable market (TAM) value could range anywhere from $625 billion to $750 billion across industries.
What obstructions exist? The cross-tech stack layer and the need for vertical or use case-specific converged solutions make managing IoT cybersecurity extremely challenging. Achievement will depend on different partners recognizing the difficulties, focusing on advancement, and settling on modern norms. Time is also needed to test and validate the solutions. Additionally, there is a global talent shortage in cybersecurity, and there is an urgent requirement for industry talent with expertise in both IoT and cybersecurity. In addition, the emerging field of cybersecurity incorporates IoT skill sets.
Nevertheless, there are grounds for optimism. The approaches that top cloud providers like Google, Microsoft, and Amazon Web Services take to IoT security have increased. Security is now a top priority for semiconductor players like Intel and Qualcomm Technologies, whose products power crucial IoT devices and networks. In recognition of the significance of security, pure-play IoT technology providers like Cisco Systems and Samsara provide distinct IoT security solutions. Lastly, a few companies, like BlackBerry and Siemens, are well-positioned to combine enterprise cybersecurity solutions with IoT platforms because they are at the intersection of cybersecurity and the Internet of Things.
For close to a decade, McKinsey has surveyed businesses and decision-makers worldwide regarding the Internet of Things and actively participated in discussions regarding its potential and challenges. The firm’s experts have sought to comprehend the transformative value of connecting the physical and digital worlds through the Internet of Things (IoT) plumbing. This work has repeatedly led us to the conclusion that enormous value can be realized when broad societal benefit, utility, and productivity are taken into consideration. By 2030, we anticipate a total potential of between $5.5 trillion and $12.6 trillion. This has given rise to the number of IoT solution providers.
For a truly seamless experience that enables the next generation of the Internet of Things, we have put a lot of effort into understanding today’s obstacles and potential solutions. One of our conclusions is that trust and security have become more and more important barriers, but IoT and enterprise security solutions are still in their infancy.

Aimee Garcia is a senior editor at ReadDive. She has 5+ years of experience in Digital Marketing. She has worked with different IT companies.