With the increase in cybersecurity threats, vulnerability remediation is a point of focus for most companies. The existing regulations like PCI DSS, HIPAA, NIST 800-731, and more make it an absolute necessity.
For a quick reference, let’s take a look at what vulnerability remediation is and the best practices for its implementation.
What is Vulnerability Remediation?
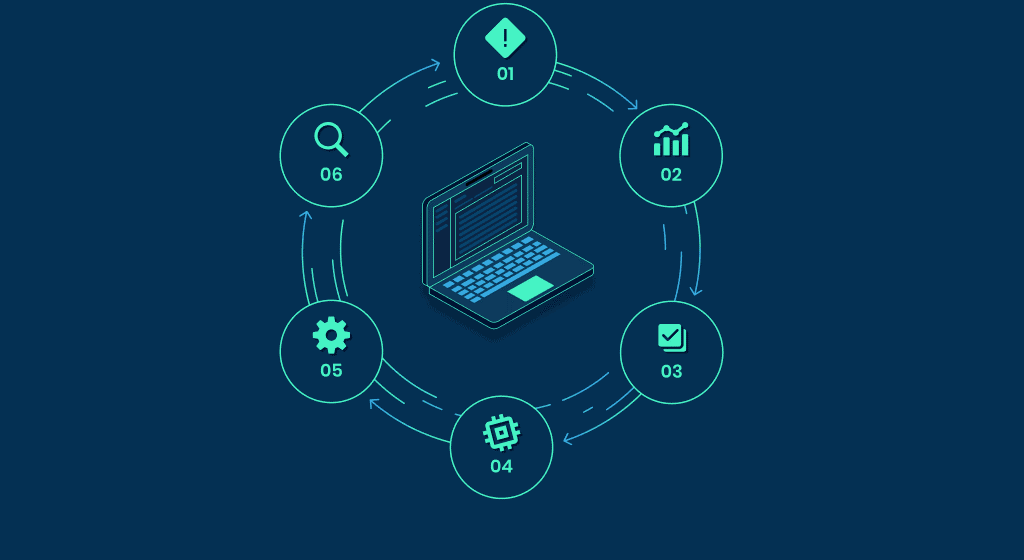
Vulnerability remediation is a crucial step in vulnerability management. So, what’s the difference?
Vulnerability management is the process of taking your network vulnerabilities and threats into account. This means finding, evaluating, prioritizing, and eliminating these threats.
Vulnerability remediation is an important step in vulnerability management as it consists of all the work done in reducing and eliminating threats. While this depends on aspects of vulnerability management, like a proper assessment of the level of threats, it is vital that steps for remediation are updated regularly.
Best Practices for Vulnerability Remediation
1. Have a Good Understanding of Your Existing Infrastructure
Create a working map of your existing network structure. This should be in the form of a map or flowchart with details about the hardware, software, and cloud computing options.
Identify which devices and programs communicate with each other and the personnel responsible for the operation of each.
2. The Right Scanning Tools
There are a lot of vulnerability scanners available in the market. Choose one that meets your demands and can identify potential attacks correctly.
● Continuous Scanning
New technology is adapted into existing workflows with astonishing speed. It is vital that you keep up with this tech and its associated risks. Make sure you proactively implement tools to scan networks and endpoints continuously.
● Choose Authenticated Software
Authenticated software read devices and software correctly without the need for any guesswork. Give access to legal software and tools.
● Observe Both Internal and External Processes
It is important to make sure you are aware of threats both inside and outside the organization. Internal scans help you block lateral threats within your network while external scans prevent hackers from exploring loopholes.
3. Patching is Not the Solution
There should be solutions to security concerns that are not limited to patching. Configuration management and compensating controls, including steps like shutting down a process, session or module, should also be used in combination with patches. The best combination differs according to the vulnerability in question. There is also a possibility of using third party data or utilizing the company’s experience with similar vulnerability.
4. Priorities the Threats Being Addressed
Instead of trying to solve threats one by one or as they come, develop an efficient system to prioritize the order in which threats should be addressed.
- Make sure you prioritize the threats that would have a higher impact on your operations. Think about day-to-day operations that would be affected if the risks are exploited. Make sure these threats are fixed first.
- The skill level required to exploit this threat should be taken into account. Those threats that can be exploited through automation or low skill hackers need to be focused upon.
- Make sure that vulnerabilities that put user data or client information at risk are plugged immediately. Also, ensure that older vulnerabilities are fixed.
- Ensure that fixing one risk won’t affect other hardware or software adversely.
5. Involve Your Team
Make sure your entire team is involved in the process of vulnerability remediation. This would ensure widespread practices that are implemented throughout the organization. About 90 percent of all cyberattacks could have been prevented by changes in employee behavior.
These are some basic steps in vulnerability remediation that could go a long way in preventing cyberattacks and protecting important company data.
Read Dive is a leading technology blog focusing on different domains like Blockchain, AI, Chatbot, Fintech, Health Tech, Software Development and Testing. For guest blogging, please feel free to contact at readdive@gmail.com.